When the Voice of the Customer Actually Talks
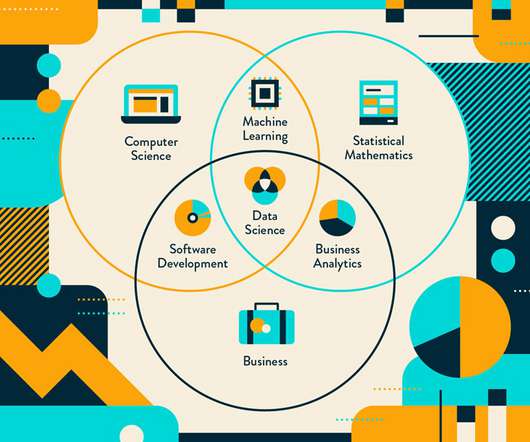
Rocket-Powered Data Science
AUGUST 22, 2021
The goals of such activities are to improve customer service, customer interactions, customer engagement, and customer experience (CX) through just-in-time customer assistance, personalization, and loyalty-building activities.






















Let's personalize your content