AI and cybersecurity: A double-edged sword
CIO Business Intelligence
JANUARY 21, 2025
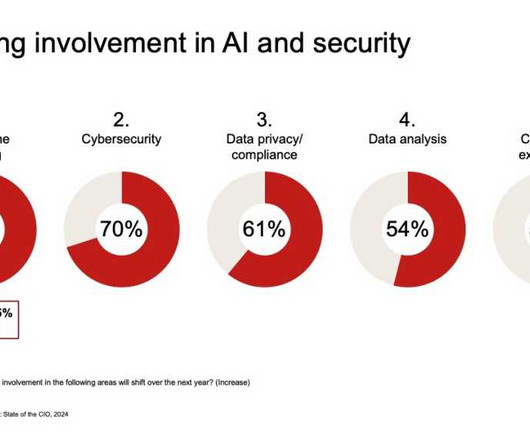
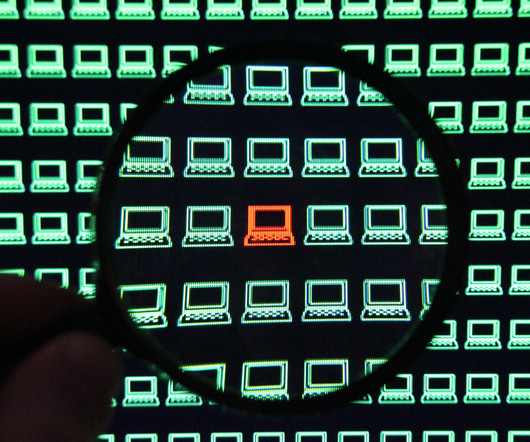
Perhaps one of the most anticipated applications of AI in cybersecurity is in the realm of behavioral analytics and predictive analysis. By leveraging machine learning algorithms, AI can analyze user behavior and network traffic patterns, identifying anomalies that might indicate insider threats or other malicious activities.


















Let's personalize your content